In the dynamic world of technology, the concept of a wallet has dramatically evolved beyond its traditional form. Previously confined to leather or canvas materials for holding cash and coins, wallets have now embraced the digital era. This transformation mirrors the shift from physical currency to digital payment methods, including credit and debit cards. However, the advent of smartphones has catapulted wallets into the digital realm, introducing us to the convenience of mobile wallet applications.
One notable advancement in this digital transformation is the emergence of crypto wallets. Distinguished by their ability to interact with blockchain technology, crypto wallets manage the private keys essential for cryptocurrency transactions. They exist in various forms, including desktop and mobile apps, and even as physical devices, offering versatility to users across the globe.
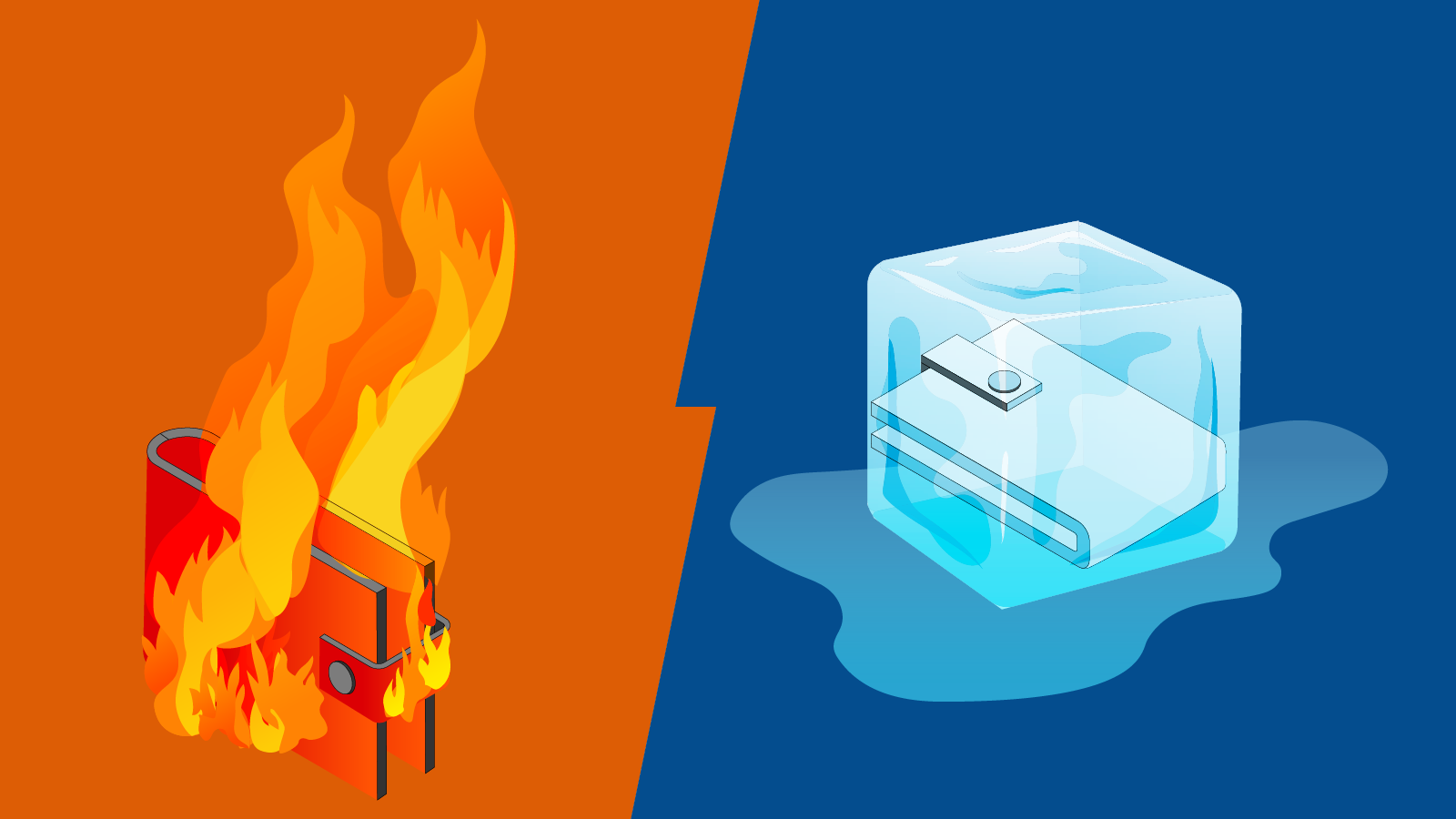
To demystify crypto wallets, we delve into their primary categories: custodial, non-custodial, hot, cold, warm, smart contract, MPC (multi-party computation), and multi-signature. Our focus will narrow on hot, cold, and warm wallets, particularly for institutional investors, providing a clearer understanding of their functionalities and security features.
Hot Wallets: The Gateway to Cryptocurrency Transactions
Hot wallets are digital wallets that maintain a constant connection to the internet. This feature is their defining characteristic, offering users the convenience of instant access to their cryptocurrency holdings for quick transactions. Unlike their cold wallet counterparts, hot wallets are designed for everyday use, facilitating seamless exchanges, transfers, and access to various blockchain services.
The Convenience Factor
Easy Setup and Use
The primary appeal of hot wallets lies in their user-friendly nature. Platforms like MetaMask exemplify this, enabling users to interact with the Ethereum blockchain within minutes of setup. Their integration into browsers and mobile apps simplifies the process of sending and receiving tokens, highlighting their role as a vital tool for retail investors venturing into the crypto world.
Integration with Crypto Applications
Hot wallets serve as more than just storage; they're a key for accessing decentralized applications (dApps). They allow users to sign in to various crypto services, making them indispensable for developers and users alike. This ease of integration promotes a vibrant ecosystem where hot wallets act as a bridge between traditional internet activities and blockchain-based interactions.
Security Concerns
Vulnerability to Threats
The internet connectivity of hot wallets, while convenient, exposes them to cyber threats. Phishing attacks targeting wallet keys are common, with scammers employing sophisticated tactics to deceive users. The case of MetaMask phishing attempts underscores the importance of vigilance and the adoption of best practices for digital security.
To counter the inherent risks, users are advised to store only minimal amounts necessary for transactions in hot wallets. This approach minimizes potential losses in the event of a security breach. Furthermore, utilizing additional security measures, such as two-factor authentication (2FA) and regular monitoring of account activity, can significantly enhance the safety of hot wallet holdings.
Popular Hot Wallet Options
Several hot wallets have gained popularity due to their ease of use, security features, and wide acceptance across the crypto landscape. Examples include:
MetaMask: Highly favored for its simplicity and compatibility with the Ethereum network.
imToken: Offers a robust mobile experience with support for multiple blockchains.
Trust Wallet: Known for its user-friendly interface and multi-currency support.
Phantom: A preferred choice for Solana blockchain users, emphasizing security and ease of access.
Cold Wallets: The Gold Standard for Cryptocurrency Security
Cold wallets, also known as offline wallets, are designed to store cryptocurrency away from the vulnerabilities associated with internet connectivity. This category includes hardware wallets, paper wallets, and other forms of storage that do not require an active internet connection. By being offline, cold wallets provide a fortress-like security level against cyber attacks, making them an ideal choice for long-term storage of digital assets.
Unparalleled Security
Protection from Online Threats
The primary advantage of cold wallets lies in their immunity to online hacking attempts, phishing scams, and other digital threats. Since these wallets do not interact with the internet, the avenues for unauthorized access are significantly reduced. This isolation from the web makes cold wallets the safest option for securing large amounts of cryptocurrencies.
Physical Control Over Assets
Users of cold wallets enjoy complete physical control over their digital assets. Hardware wallets, for example, allow individuals to store their private keys in a physical device that can be kept secure in a safe or other secure locations. This level of control is reassuring for investors who wish to have tangible ownership of their digital wealth.
Considerations and Challenges
Convenience vs. Security Trade-off
While cold wallets offer superior security, they come at the cost of convenience. Initiating transactions with a cold wallet requires additional steps, including connecting the device to an internet-enabled computer or scanning QR codes from a paper wallet. This process can be cumbersome for those who frequently trade or use their cryptocurrency for daily transactions.
Risk of Physical Damage or Loss
Although cold wallets are safe from online hackers, they are susceptible to physical risks. Hardware wallets can be damaged, lost, or stolen, while paper wallets can deteriorate or be destroyed. Users must take precautions to safeguard their cold storage devices against such incidents, often requiring backups or secure storage solutions.
Popular Cold Wallet Options
A variety of cold wallets are available, catering to the needs of different users. Some of the most trusted and widely used include:
Ledger Nano S and X: Renowned for their robust security features and support for multiple cryptocurrencies.
Trezor Model T: Offers a touchscreen interface for enhanced usability without compromising security.
Paper Wallets: While less common, they provide a simple and effective way to store crypto offline. Websites like walletgenerator.net offer tools to create them securely.
Warm Wallets: Balancing Convenience and Security
Warm wallets represent a middle ground between the hot and cold wallet extremes, offering a blend of the convenience found in hot wallets with the enhanced security measures typical of cold wallets. They are designed to be connected to the internet, yet incorporate additional security features to mitigate the risks associated with online storage. This unique combination makes warm wallets an appealing choice for users seeking both practicality and safety in managing their cryptocurrency assets.
Advantages of Warm Wallets
Enhanced Security Features
Warm wallets stand out by integrating advanced security technologies such as multi-signature authentication, multi-party computation (MPC), and smart contracts. These features add layers of protection, making warm wallets less susceptible to the vulnerabilities that affect traditional hot wallets. For instance, multi-signature wallets require more than one private key to authorize a transaction, significantly reducing the risk of unauthorized access.
Convenience for Regular Use
Despite their added security, warm wallets maintain a level of convenience that allows users to engage with the blockchain ecosystem efficiently. This balance is particularly beneficial for users who frequently transact in cryptocurrencies but are also conscious of the security risks inherent in hot wallets. Warm wallets provide a practical solution for day-to-day transactions without compromising on safety.
Considerations for Users
Navigating the Security-Convenience Spectrum
Users of warm wallets need to consider their specific needs and risk tolerance when choosing the right wallet type. While warm wallets offer a compromise, they may still present challenges for those unfamiliar with the additional security mechanisms. The choice between hot, cold, and warm wallets ultimately depends on the user's transaction frequency, the volume of assets managed, and their security preferences.
Staying Informed and Vigilant
As the cryptocurrency landscape evolves, so do the tactics employed by malicious actors. Users of warm wallets must stay informed about the latest security best practices and remain vigilant against potential threats. Regularly updating wallet software, using secure and unique passwords, and understanding the technology behind warm wallets are essential steps in safeguarding digital assets.
Popular Warm Wallet Examples
Several warm wallets have gained popularity for their innovative approaches to combining security with usability. Notable examples include:
Fireblocks: Offers an MPC wallet solution catering to institutional users, emphasizing security without sacrificing transaction efficiency.
Argent: Integrates smart contract technology to enable wallet recovery features, making it a secure and convenient option for Ethereum users.
CoinsDo: Leverages MPC technology for decentralized custody, offering secure and instant cross-chain transactions.
The Right Choice for Institutions
For institutions managing substantial cryptocurrency portfolios, the imperative to devise a comprehensive and secure asset management strategy cannot be overstated. As these entities expand, both in operational scope and asset volume, the complexity of safeguarding their digital wealth intensifies. Emulating practices adopted by seasoned retail investors and tailoring them to fit an institutional framework is not just advisable; it's essential for the longevity and security of their investments.
A nuanced approach, integrating a variety of wallet types, emerges as a prudent strategy for institutions navigating the intricate landscape of cryptocurrency management. This methodology acknowledges the distinct security and operational requirements inherent to different sizes and types of institutions.
Consider, for instance, the case of a burgeoning tech startup that has successfully secured $5 million in funding. With a lean team of fewer than ten employees, including its founders, the company stands at a crucial juncture where effective asset management is pivotal.
Cold Wallet - Store 60% of Your Funds Here
A strategic allocation of its funds—60% in a secure, company-owned cold wallet—would safeguard the majority of its capital from the omnipresent threats of cyberattacks and unauthorized access, leveraging the unparalleled security benefits of offline storage.
Warm Wallet - Store 30% of Your Funds Here
Meanwhile, earmarking 30% of the funds for a warm wallet, controlled by the founders, strikes a balance between accessibility and security. This portion allows for operational flexibility, enabling timely investments and transactions while employing advanced security measures to mitigate risk.
Hot Wallet - Store 10% of Your Funds Here
The remaining 10%, distributed across various hot wallets, addresses the day-to-day operational needs of the business. These funds are readily available, facilitating quick transactions, payments, and the seamless use of blockchain services essential for the startup's activities.
This diversified wallet strategy not only enhances the overall security posture of the institution but also provides a scalable model that can adapt to the evolving demands of the business and the broader crypto market.
Navigating the World of Crypto Wallets
The evolution of digital wallets from simple physical carriers to sophisticated cryptocurrency management tools reflects the broader transformation within the financial and technological landscapes. As we've explored, the choice between hot, cold, and warm wallets is not merely a matter of preference but a critical decision that impacts the security and convenience of managing digital assets.
Choosing the right wallet type is a foundational step in your cryptocurrency journey. It requires an understanding of your transaction habits, security tolerance, and the specific features each wallet type offers. Whether you prioritize ease of access, security, or a balance of both, there is a wallet solution designed to meet your needs.